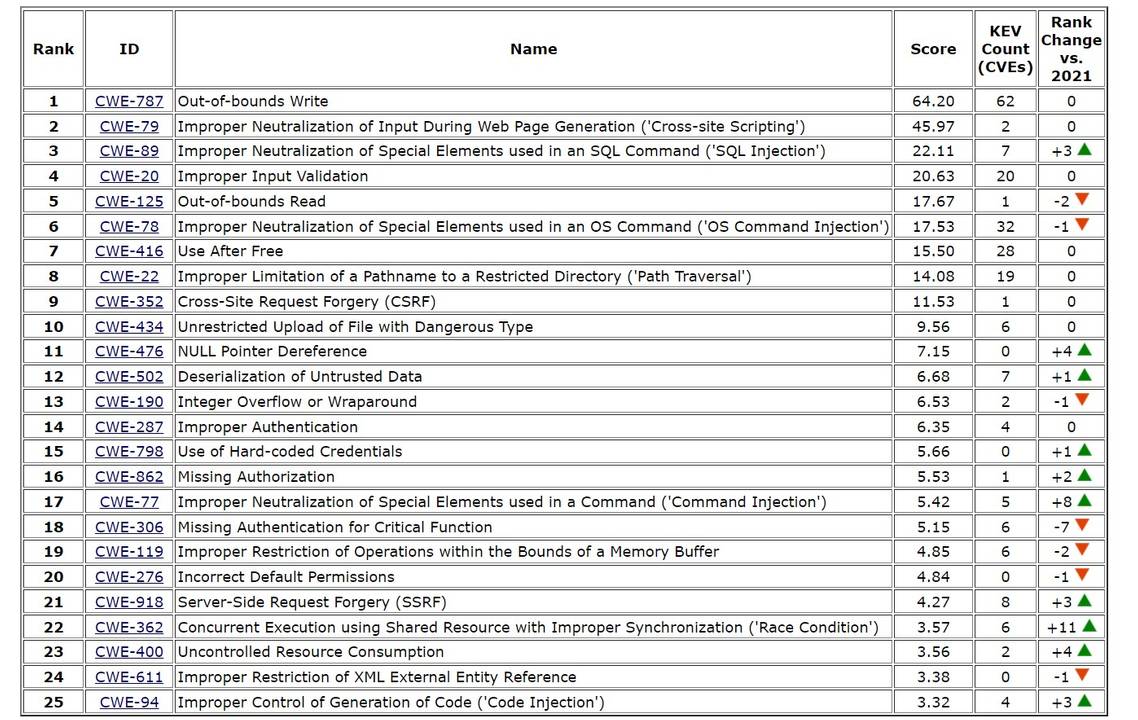
The US Cybersecurity and Infrastructure Security Agency (CISA) and non-profit MITRE which manages federally funded research in cybersecurity, have released the 2022 Common Weakness Enumeration (CWE) Top 25 Most Dangerous Software Weaknesses list. An attacker can exploit these vulnerabilities to take control of an affected system, obtain sensitive information, or cause a denial-of-service condition.
This year’s list also incorporates updated data for recent Common Vulnerabilities and Exposure (CVE) records in the dataset that are part of CISA’s Known Exploited Vulnerabilities (KVE) Catalog launched in November 2021. In total, the dataset analysed contained a total of 37,899 CVE Records from the previous two calendar years.
As with past years, there is a continued transition in the Top 25 to more specific Base-level weaknesses, while there is a slow decline in the number of unique Class-level weaknesses (from 9 in 2020 down to 7 in 2022). This movement is expected to continue in future years as the community improves its mappings to more precise weaknesses that threaten today’s systems at a more operational level, as Base-level weaknesses are more informative to practical mitigation than higher, Class-level weaknesses.
Regarding risk mitigation, CISA said that this year’s list would benefit software architects, designers, developers, testers, users, project managers, security researchers, educators, and contributors to standards developing organisations.
The full report is available at: https://cwe.mitre.org/top25/archive/2022/2022_cwe_top25.html